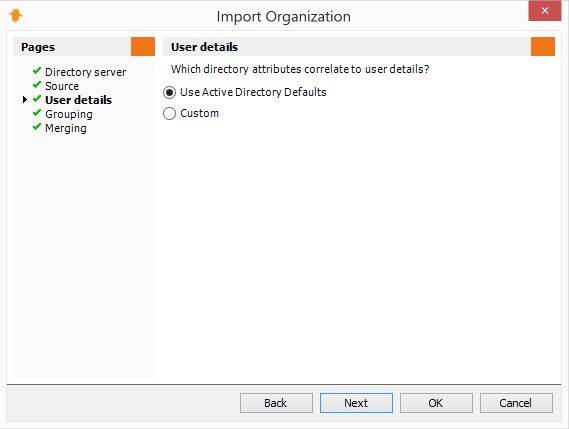
Importing your Organization from LDAP
The Import Organization Wizard is the quickest way to import your existing users and from Active Directory along with any attribute or OU to create Groups.
To get started, click the Organization tab, and then click the Import Organization link to launch the Import Organization from LDAP wizard.
Tip: It is a good idea to automate the Import Organization from LDAP action before any scheduled reports. To avoid having to configure the Import Organization settings over again, go to Tasks, select your scheduled task and click Add | Import Organization from LDAP.
The Import Organization from LDAP Wizard will guide you through the process of making the following selections:
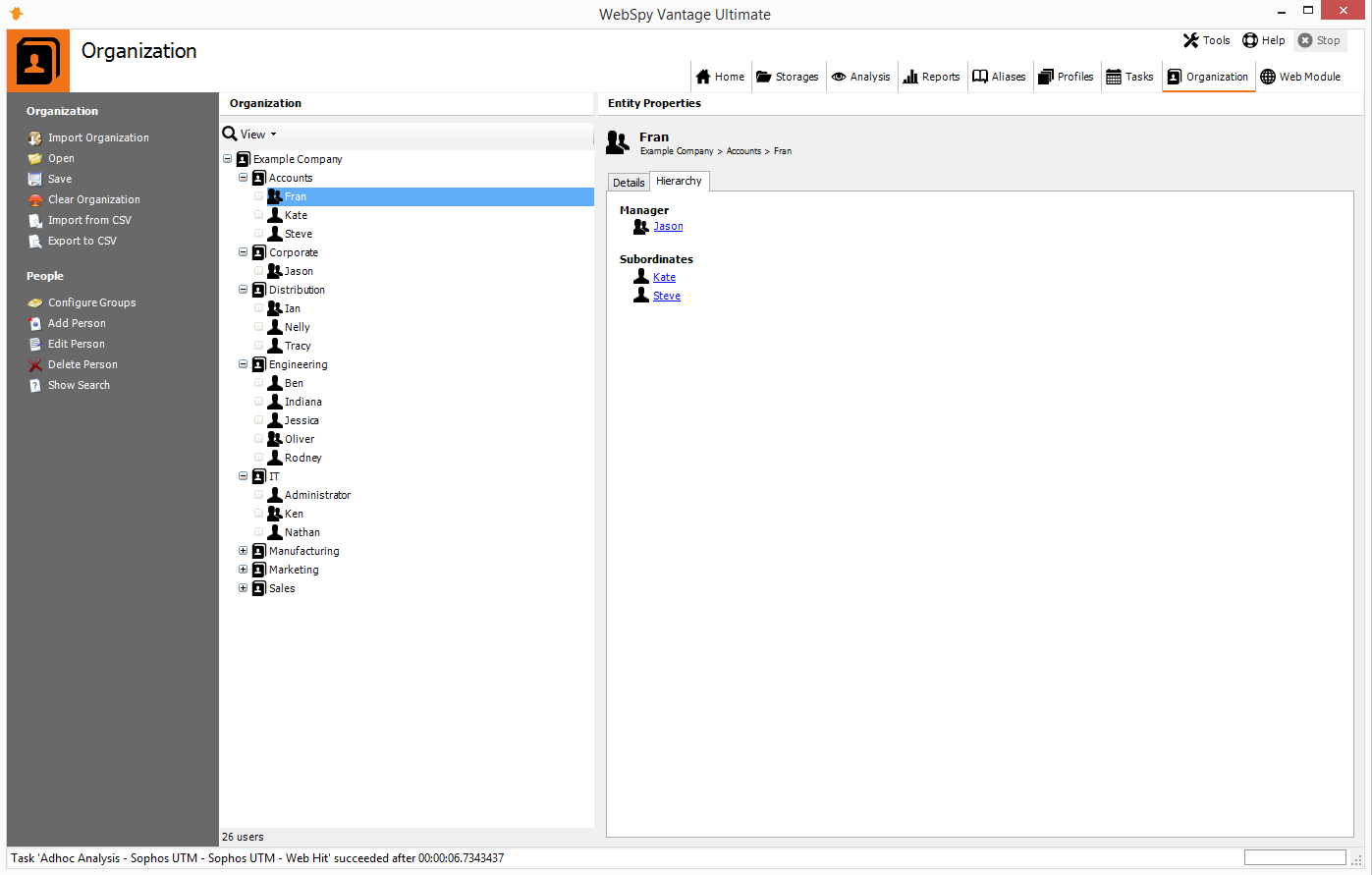
Directory server
On the Directory server page, select LDAP from the Type dropdown list. If your WebSpy Vantage server does not have a network connection to your directory server, you can export your directory to an LDIF file, and then select LDIF from the Type drop down list.
Select your directory along with the credentials of an account that is authorized to query the directory (usually, any domain account in domain\username format) then click Test. Click Next after you have successfully connected to your directory server.
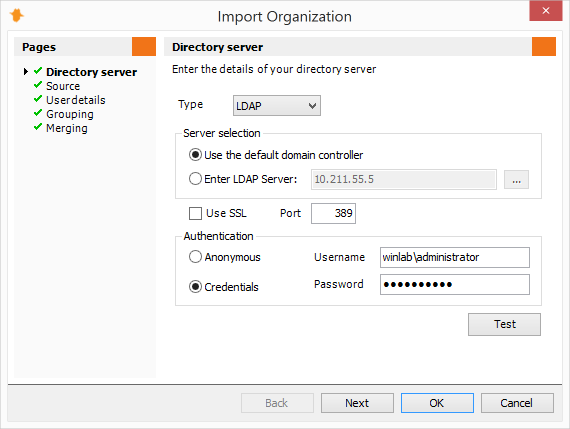
Source
On the Source page, select a Root Distinguished Name to search for users within (for example, 'dc=mydomain, dc=com'). If your users are contained within a specific OU, select the ‘…‘ button to select the OU in your directory.
The LDAP search query defaults to a basic query that returns 'user objects', however you can change this if necessary to reduce the number of users imported (WebSpy Vantage's licensing is based on the number of users imported). Use the Quick Queries dropdown to change the LDAP search query to import a more specific set of user accounts, such as enabled users with an email address.
WebSpy Vantage will import all users up to your license limit, which is unlimited during your trial. Click Next.
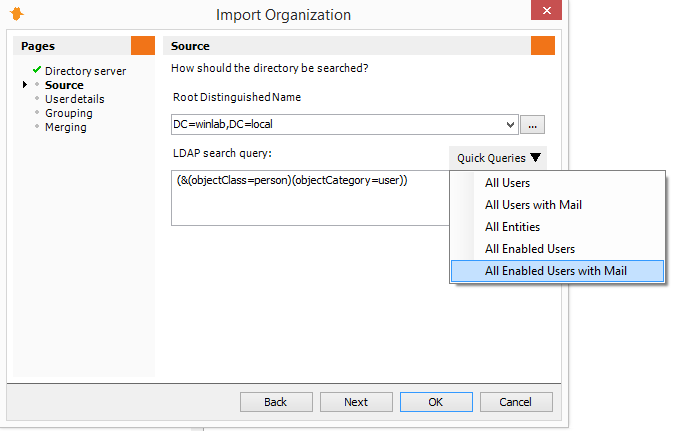
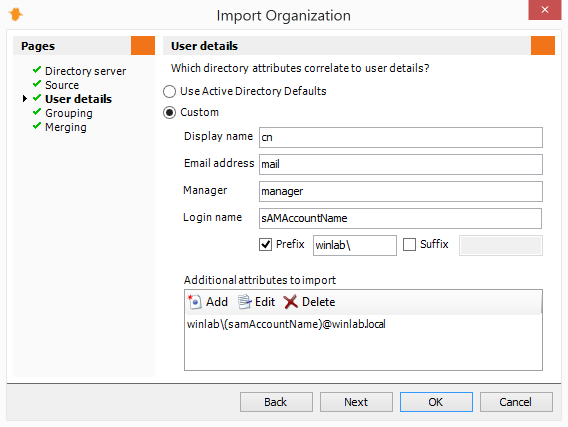
User Details
The User Details page defines how Vantage maps user objects in your Directory to authenticated usernames in your log files, as well as configuring user login names for the Web Module, the email address to send report notifications to, and the attribute to use to find a user’s manager.
If you are using Active Directory, you can choose Use Active Directory Defaults. This will import the most common username formats both with and without domain prefixes accounting for 99% of log analysis situations that we see.
If you are using a different directory server, or your log file record usernames in a custom way (such as a custom UID), then select Custom.
There are two important concepts:
Login Name:
Usually, you will configure the Web Module to use Windows Authentication. For your users to be able to login using this authentication method, specify a prefix in the login section for yourdomain\ (replace with your actual domain and include the slash).
IIS will then authenticate your users against your domain correctly, and they will be able to login to the web module without an authentication prompt as long as they’re logged into Windows, assuming they’re permitted login to the Web Module (see the Configure Web Module Permissions section below).
Know your log file’s username format:
The configuration of the User Details page defines what is imported into the Usernames Alias (seen on the Aliases tab), which is what maps the authenticated usernames in your log files to user objects in your domain.
You can utilize the Usernames Alias in the content of your reports (via nodes in Report Templates), and when specifying Filters when generating reports (via Add | Field Value Filter | Summary = User, Alias = Usernames).
Log files record authenticated usernames in a variety of ways. Some simply log the login name (called sAMAccountName in Active Directory), some include the domain prefix (Domain\sAMAccountName), some include an authentication realm suffix (Domain\sAMAccountName@Realm) and so on.
It is important to know how your device is logging usernames, so that you can prefix and/or suffix the appropriate values around the sAMAccountName, or import a different attribute from your directory such as userPrinicpalName, a UserID or the user’s full DN.
To find out how your device logs usernames:
- Go to the Analysis tab and run an ad-hoc analysis and your storage (add a Date Filter on the Filters page to keep the analysis small), and then go to the Usernames summary in the analysis.
- Note the username format, and use the appropriate options in the User Details page of the Import Organization wizard.
If your device logs in the Domain\Username format, use the ‘prefix’ option in the Login name section to prefix yourdomain\.
If your device logs usernames differently, click the Add button in the Additional Attributes section, and enter the attribute you would like to import from your domain (such as sAMAccountName or UID), and use the prefix/suffix options to surround the imported value with the appropriate text.
Once you have configured the User Details page to create an appropriate login name, as well as map user objects to your log data, click Next.
Grouping
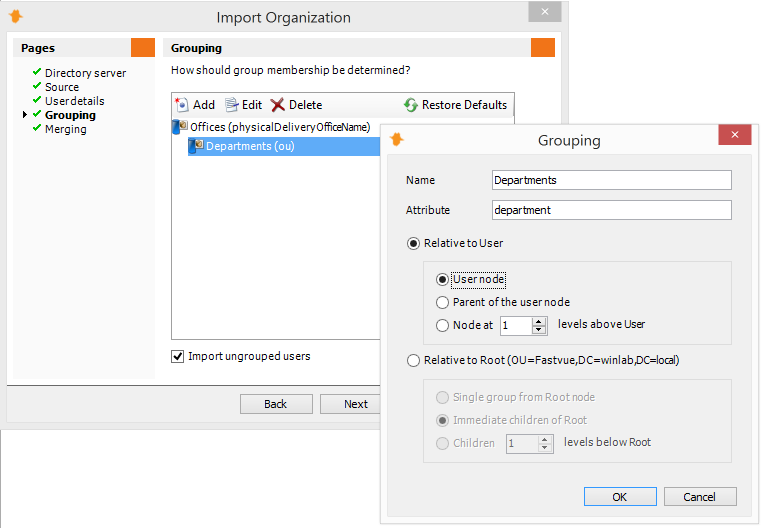
The Grouping page enables you to configure how you would like users grouped, such as by Departments, Offices, OUs etc. User Objects in Active Directory have a number of attributes, including department, office, description, company, and you can also place user objects in OU containers, and configure attributes on those containers. WebSpy Vantage can hook into any of these attributes to group your users for the purpose of reporting.
By default, there are two groups specified: Offices (using the physicalDeliveryOfficeName attribute in Active Directory) and Departments (using the department attribute in Active Directory). You can edit or delete these groups as necessary.
When adding or editing a group:
- First, enter the name of the Group into the Name field. This is up to you and should represent what the group is, such as ‘Departments’, ‘Locations’, ‘Business Centers’ etc. (Note, there are a few default Report Templates that use ‘Departments’ so use the word ‘Departments’ in one of your grouping levels utilize these reports).
- Enter the exact name of the attribute into the Attribute field. For example, enter
physicalDeliveryOfficeNameto import the Office attribute from Active Directory. To import the name of an OU, use the attributeOU.
Note that by default, Active Directory Users and Computers hides the real attribute names. You can change this by selecting View | Advanced Features to show the Attribute Editor with real attribute names when editing a User or OU).
There are two ways to specify the object in your directory that contains the attribute to use for grouping:
- Relative to user:
Use this option if the attribute is located on the user object itself or on one of its parent OU containers. For example, if you are using thedepartmentattribute on the user objects, then select Relative to user and select User node. Or if your users are in a consistent OU structure, specify either Parent of the user node, or Node ‘n’ levels above to access the attribute on the appropriate parent OU container. - Relative to root:
Use this option to select OUs relative to the Root Distinguished Name that you specified on the Directory Server page. For example, if you have defined OUs for all your Offices directly underneath your Root DN, with user objects located anywhere underneath those OUs, then use the Immediate children of Root option, or the Children ‘n’ levels below Root option. For inconsistent OU structures, you can use the Single group from Root node option, and use the Import Organization wizard multiple times (usually specified as part of a Task) with the Merge options set, to create groups from multiple Root DNs in your directory.
Tip: Later, you’ll need to configure Web Module access permissions for people and/or groups. To create a default set of permissions that apply to your entire organization, create a top-level group using an attribute that everyone is a member of. For example, call the group ‘Domain’ and use the attribute ‘dc’.
Once you have specified all the Groups you would like to use in your Reporting process, click Next.
Merging
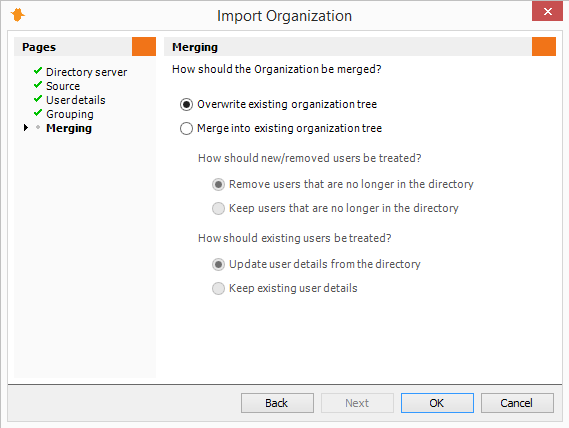
The Merging page enables you to use the Import Organization wizard multiple times, and merge the results into your existing Organization structure. For example, first import your Organization from one domain (or one Root DN on your domain), with the Overwrite existing organization tree option set to create an initial Organization tree, then run the Import Organization wizard again to import your Organization from another domain (or a different Root DN on your domain) and merge the results into your existing Organization tree.
The Merge options enable to you to keep or remove users that can no longer be found in the directory, as well as keep or update existing user’s details. Use the ‘keep users / keep details’ options if importing from a different domain or root DN.
Note: When merging, only users that have previously been added from your LDAP/LDIF directory will be affected. Users that have been manually added will not be affected.
Click OK to complete the Import Organization wizard and begin the import. Once the import is complete you will see you the Organization tree displayed. You can use the View drop-down list at the top of the Organization tree to display your groups, or your manager/subordinate hierarchy.